Sep 3 2019
Bitwings Comes As Coins Virtual Money that Secure Consumer Electronics for The Blockchain Era
WINGS MOBILE is a software developer and mobile network operator. Since 2017, the company also engaged as a manufacturer of electronic. Exceptional business management can connect the needs of every electronic user by making three-way business a daily basis. The products released also have high innovation to provide world-class technology solutions.
The company offers services to major telecommunications operators such as Jazztel (Orange), Belgacom, Ono (currently Vodafone), and Tata. The organization decides to create a distribution system to the retail market and distribute its services and products directly to customers. This poses a significant challenge to lesser-known brands, in markets traditionally played by distributors who are more likely to be the best-selling brands.
Wings Mobile uses a business model that is based on rapid development and accuracy of execution. These two things serve as the fundamental pillars of the Wings Mobile business model. The innovations from technology continue to develop continuously. The acceleration of technology development is also more intense when compared to other economic sectors. One month in the technology sector is equivalent to one year in the industrial area. The Mobile Wings development team fully understands this philosophy and participates to innovate in the technology field.
Some Software and Technology Developed
Wings have two services launched for the community, namely Wings Mobile and Wings Energy. Wings Mobile is a highly competitive virtual cellular network operator in calling services both national and international calls by avoiding additional roaming fees in sixty countries. This service is a leading service for Wings customers. Then the Energy retail service provider was created to provide natural gas and electricity supply services to individuals and companies.
Then the distribution system developed is social market wings and wings store. Some of the products that have been designed and available in the market are Wingsphones and Wings book. Also, Wings develops software and technology, including:
- Wings Secure All are secure calls that are protected by three types of security.There are ICE technology for P2P utilities, Transport Layer Security (TLS) for Internet communication, and ZRTP (Zimmermann Real-time Transport Protocol) for exchange protected by encryption keys.
- Wings Suite, is an application designed for PC and cellular users simultaneously, or for finding cellular battery power when low. This allows users to transfer all WINGS PHONE functions and GSM calls from all cellular operators on the WINGS BOOK (laptop).
- Wings Guardian is an application in the form of a security system that clearly verifies whether an app is installed or a Trojan uses a camera or microphone without the user’s knowledge.
- Wings Defender is the software to ensure high performance and safe use. This application comes with a full and powerful Antivirus integration such as Wings Defender is something that cannot ignore. By continually being updated with all types of Trojans, viruses, malware, this optimizes security and gives users full protection, as well as optimizing CPU, RAM, and battery.
- Wings Voip Call offers all Wings Phone or Wings Book owner the possibility of using exclusive VoIP services. The user will decide to make a call through the VoIP or GSM network. The Wings Backoffice is the heart of WINGS Mobile, which enables the management of commercial and distribution systems. The software manages delivery, billing, calculation and commission settlement, logistics, warehouse, payment methods, and e-commerce.
- Wings Play Store is software to offer anonymous application stores.In the regular Play Store, users must register with their Google tracks all activities and email. Wings Play is entirely anonymous, and does not require registration by email and guarantees complete privacy.
- Wings Dialer is the world’s first hybrid dialer, which integrates GSM technology with native VOIP technology. This dual system allows integration of all particular WINGS cellular functions on one dialer (keyboard). That include secure calls, free-roaming, second numbers, national and international calls with VoIP transportation, open calls, etc.
- Another exclusive service available on smartphones is Wings Second Number that allows users to choose the new telephone numbers they need, which can be used to make and receive calls with the second number as caller identification.
- Wings World Roaming is the system in the world that turns incoming GSM calls into VoIP calls, absolutely free, in a global area where there is an Internet connection. This technology works independently of the operator used by the user. Users can choose from 60 countries worldwide.
✨ Team Bitwings acknowledges and prioritizes the need for privacy in smartphones, communication and data transfer. No…
Gepostet von Bitwings am Montag, 15. April 2019
WINGS MOBILE is always very sensitive to differences and socioeconomic differences between countries. The manufacture of consumer electronic products (smartphones, PCs, etc.) is very much carried out by certain economic countries in Southeast Asia, and especially by “large factories of China.” The latter has triggered several conflicts, such as those arising from the imposition of high tariffs, which in turn have an impact on import prices in many countries, especially in developing countries. The logic of national market defense is trying to rebalance the trade balance, import and export relations of developing countries artificially.
However, it is more restrictive and impoverishing to end consumers, who are forced to pay the same product even 100% more than consumers of a country that produces that product. One way to overcome this problem might be to reduce tariffs. Ideally one must stimulate national production to go to the basic of the problem. This will not only eliminate tariff conflicts, but will boost the domestic economy by creating workplaces, valuable infrastructure, and employment.
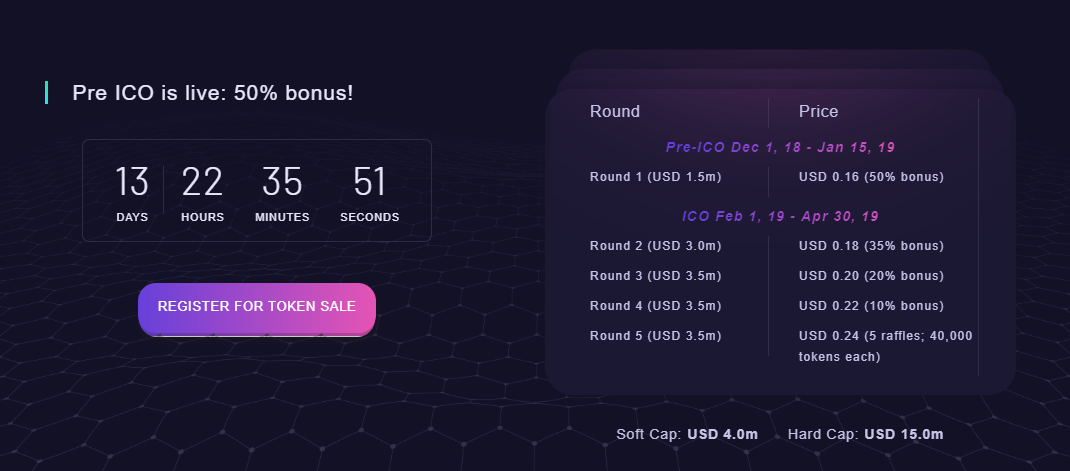
WINGS MOBILE is a company that takes focused on security technology. Therefore, in a world that is oriented and evolved towards new technology, even in commercial use, it cannot be indifferent to security issues in the cryptocurrency world. In this case, the idea of building a right WINSGMOBILE ecosystem, based on the creation of a cryptocurrency, BITWINGS comes alive. And activate, with that combination, a robust program of technological evolution and global expansion.
Bitwings & Blockchain Ecosystem
One of the strong points of differential of BITWINGS (BWN) is to base its value on the same basis as conventional currency (FIAT). Wings Ecosystem is a business space that makes WINGS MOBILE as a supplier of services and related goods. That comes to secure cellular communication, controlling the manufacturing process and innovative quality of the latest generation of technological devices and client chains. And affiliations, which connected to the ecosystem not only as users but as real business drivers who participate in the business.
The BitWings Ecosystem creates based on a growing and large geographical area. BitWings Ecosystem also based on rigorous analysis of the demand as a basis for the business model and its feasibility. The first stages have already been improving initial expectations with a very dynamic growth plan. This evolution creates a large market space on an international scale. You can take advantage of the ecosystem, it will be necessary to master reliable, but disruptive technologies that cover all phases of business. That activity may including finance, develop alternative distribution formulas, and create new payment instruments using blockchain technology that is universal and secure.
Now you can find great products for the future with blockchain technology.You may visit the website to know more about these products. Now, the world is in your grasp. Only with one click, you can do anything just with future Smartphone.












Jan 22 2020
Same Problem, Different Drivers: 2019 is Breaking Records for Data Breaches
Some types of cyber threats run together in many people’s minds. However, the question of what is a data breach versus a different type of cyber incident is pretty clear.
Data breaches have become a daily occurrence. Many organizations collect massive amounts of data about their customers and fail to properly secure these collections. Since this data is valuable on the black market, cybercriminals take advantage of these weak protections to steal sensitive data.
It probably should not come as a surprise that the threat of the data breach is not only ongoing but growing. Organizations still have the same vast collections of sensitive data, and it is only becoming more valuable. However, while the growth of the number of data breaches and exposed records in 2019 is to be expected, the drivers behind the exposure of sensitive data may be less so.
The Threat of the Data Breach
Data breaches have entered the public consciousness as one of the biggest cybersecurity threats in existence. They probably would have the top spot unopposed if it wasn’t for the very visible and personal threat of ransomware.
For many organizations, preventing a data breach is one of their highest cybersecurity priorities. With the passage of new data privacy laws like the General Data Protection Regulation (GDPR) in the European Union, the California Consumer Privacy Act (CCPA), and dozens of others, being the victim of a data breach can be extremely costly for an organization. This has created some odd incentives in cybersecurity efforts like bug bounty programs, where extremely common threats like cross-site scripting (XSS) that don’t often result in data breaches are assigned much lower bounties than rarer threats that could result in a major, public breach.
Protecting against data breaches is difficult because they can be performed in so many ways. A common cause of a data breach is misconfigured security settings in the cloud, where a “public” data store is fully accessible to anyone who can learn the URL. Data breaches are also commonly caused by exploitation of web application vulnerabilities (including XSS) that take advantage of the fact that these web apps often have direct access to back-end databases containing user account information.
Organizations attempting to protect themselves from the threat of data breaches must struggle with the fact that a data breach can be very profitable for an attacker and is difficult to defend against due to the wide range of possible attack vectors. Since the majority of organizations lack the level of technical knowledge and expertise held by many cybercriminals, and the identification of vulnerabilities that can be used in data breaches can be performed in an automated fashion, it shouldn’t be surprising that the number of data breaches is growing.
Data Breaches Continue Growing
2019 is a bad year for data breaches. In the first nine months of 2019, there were a total of 5,183 different data breaches with 7.9 billion records exposed. This represents a significant growth in both the number and impact of data breaches compared to the same period in 2018. The number of breaches has grown by 33%, and the total number of breached records is 12% higher.
Interestingly, the drivers between the number of breaches and the volume of breached records differ. Unsurprisingly, cybercriminals were responsible for the majority of data breaches; however, they don’t account for the majority of breached records.
Accidental data leaks, like those caused by misconfiguration of cloud services security settings, have caused over 6 billion records to be exposed in the first three quarters of 2019. This number is calculated based upon the number of insecure cloud data repositories that have been discovered and reported. However, the true amount of data exposed on these cloud deployments is likely much higher, and the nature of the cloud means that organizations with insecure cloud resources may not even be aware if they have been accessed by unauthorized parties.
How to Protect Sensitive Data
Data breaches can be carried off in a wide variety of different ways. Many of them are intentional actions by cybercriminals attempting to gain access to sensitive data for their own use or for resale on the black market. However, others occur without malicious intent as companies accidentally expose their own data due to negligence or a lack of understanding of how to secure new environments like the cloud.
Protecting against data breaches requires the ability to identify and monitor repositories of sensitive data through the organization’s environment. While the organization’s main databases may be well-protected, unforeseen circumstances can cause sensitive data to be stored in unprotected repositories.
Data may be migrated to the cloud to fulfill business needs, but without the oversight of the organization’s IT and security teams. Sensitive data may be needed to test software under development and be copied to a database within the development environment. The organization may have backup systems in place to protect against ransomware but inadequately protect those backups.
These unofficial data repositories are a favorite target of hackers since they lack the defenses of the main database. Protecting against data breaches requires visibility and security into all of an organization’s sensitive data, wherever it may be located.
By admin • Technology • Tags: business, cyber threats, European Union, hackers, information, market, Protect Sensitive Data, software, URL, XSS